The Role of eBPF/XDP in Next-Generation Network Security
eBPF and XDP move detection and enforcement into the kernel — running at line rate, harder to tamper with, and uniquely suited to OT/IoT boundary defense.
Expert perspectives on OT/IoT security, compliance, and threat intelligence.
eBPF and XDP move detection and enforcement into the kernel — running at line rate, harder to tamper with, and uniquely suited to OT/IoT boundary defense.

Why OT alert fatigue is structurally worse than IT — and how AI-first detection turns alert floods into a handful of high-confidence detections.
Manufacturing absorbs 27.7% of all cyberattacks. Discover 4 real-world OT threat scenarios targeting smart factories — and how to defend against them.
The Dragos 2026 OT Cybersecurity Report revealed organizations lack the telemetry to detect OT threats before operational impact occurs.
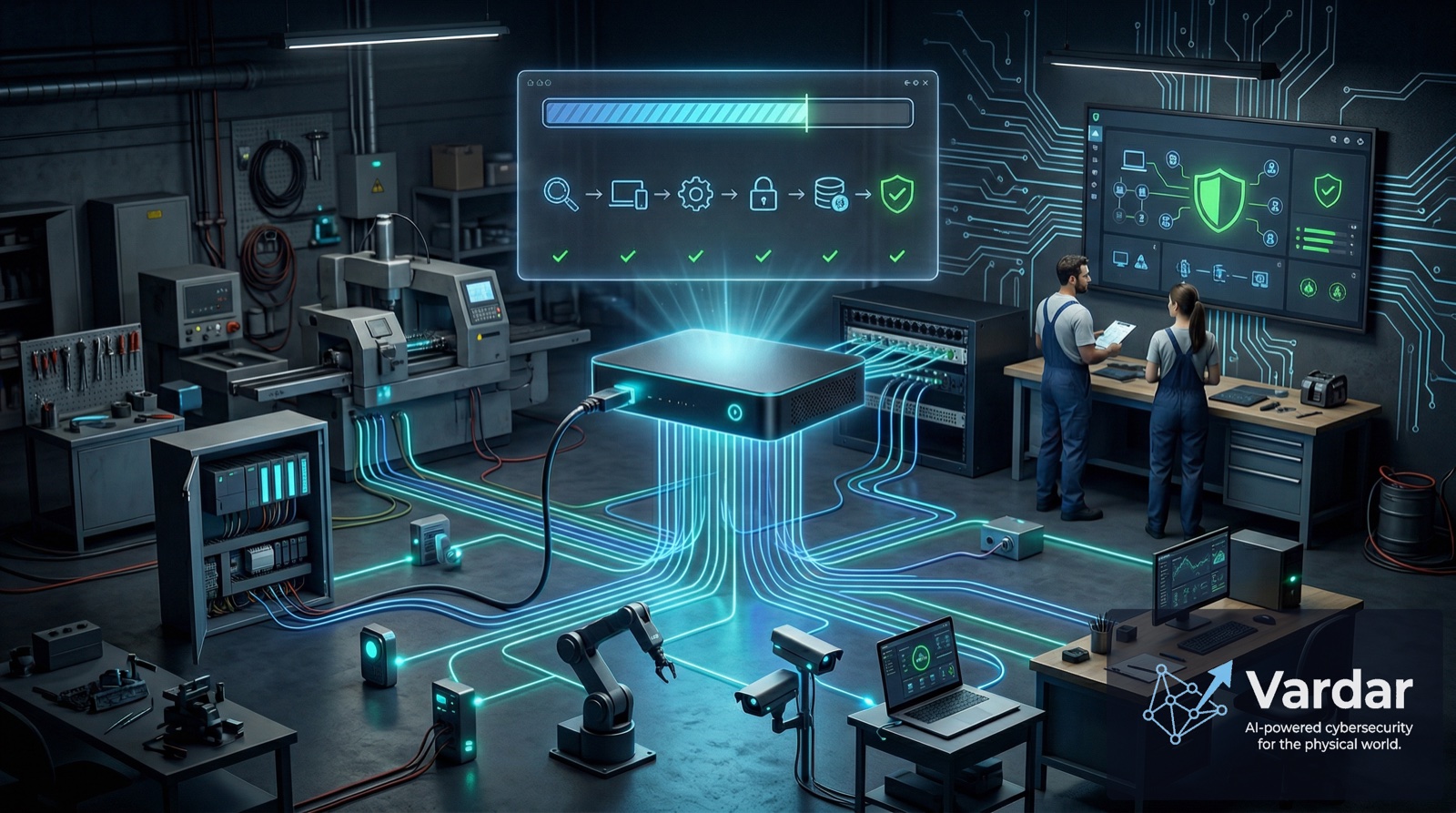
Cybersecurity is now the #1 threat facing SMBs, yet 84% self-manage with insufficient expertise. Zero-touch deployment changes that.
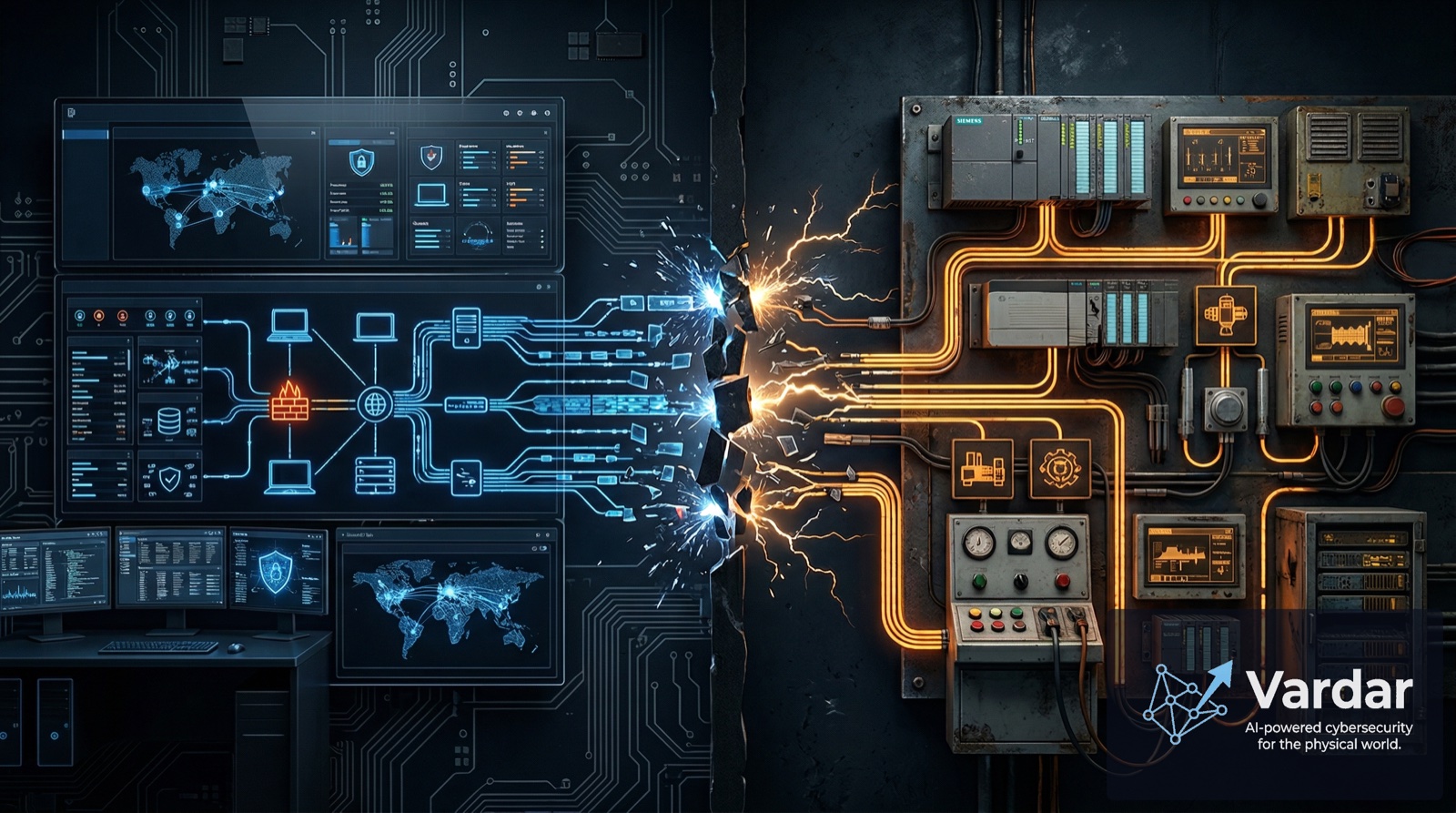
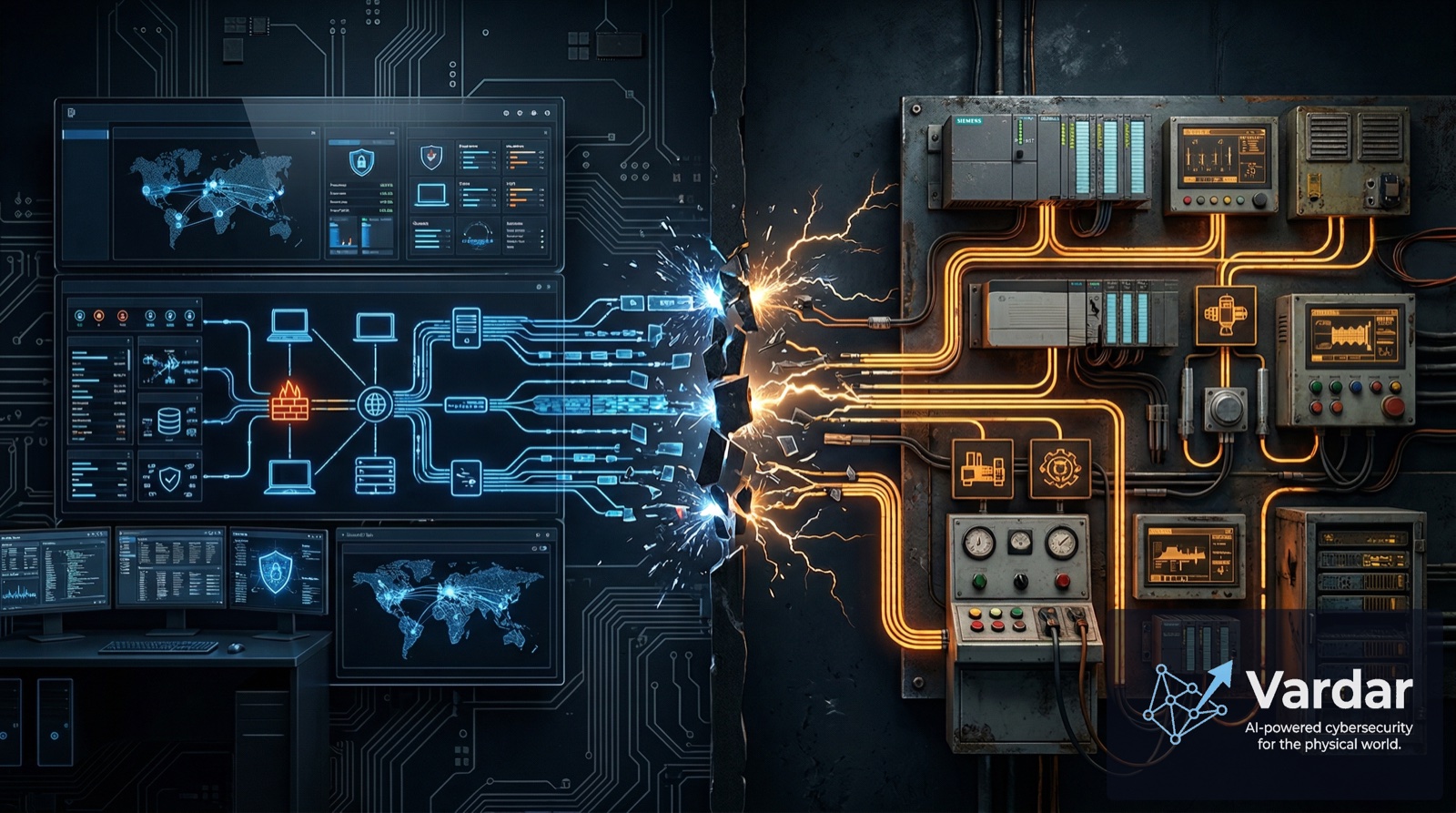
A persistent belief that IT security tools can extend to OT environments is getting organizations breached — and the data proves it.
Half of OT organizations were breached last year despite advancing their security programs. Collective threat intelligence is the missing piece.
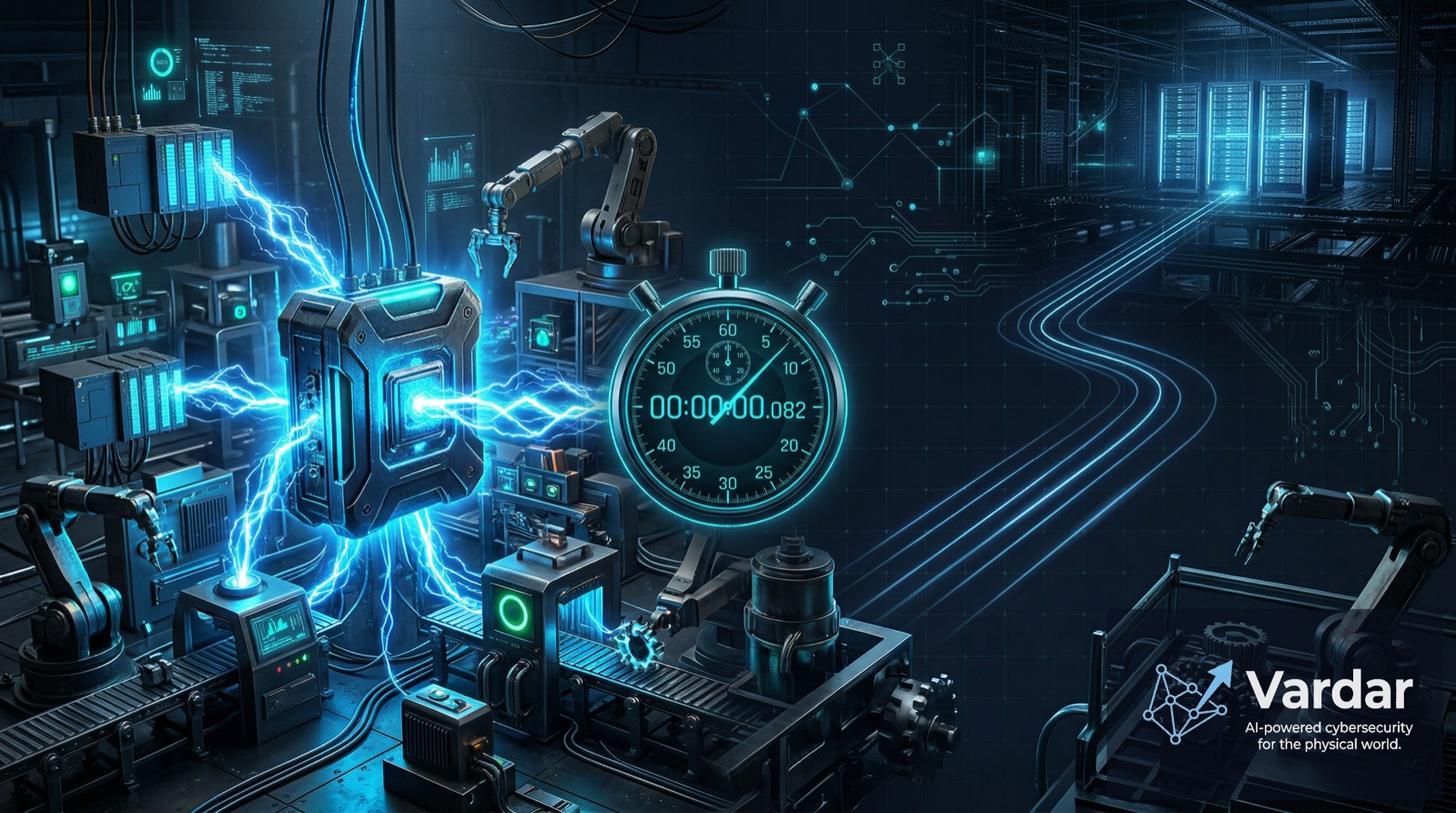
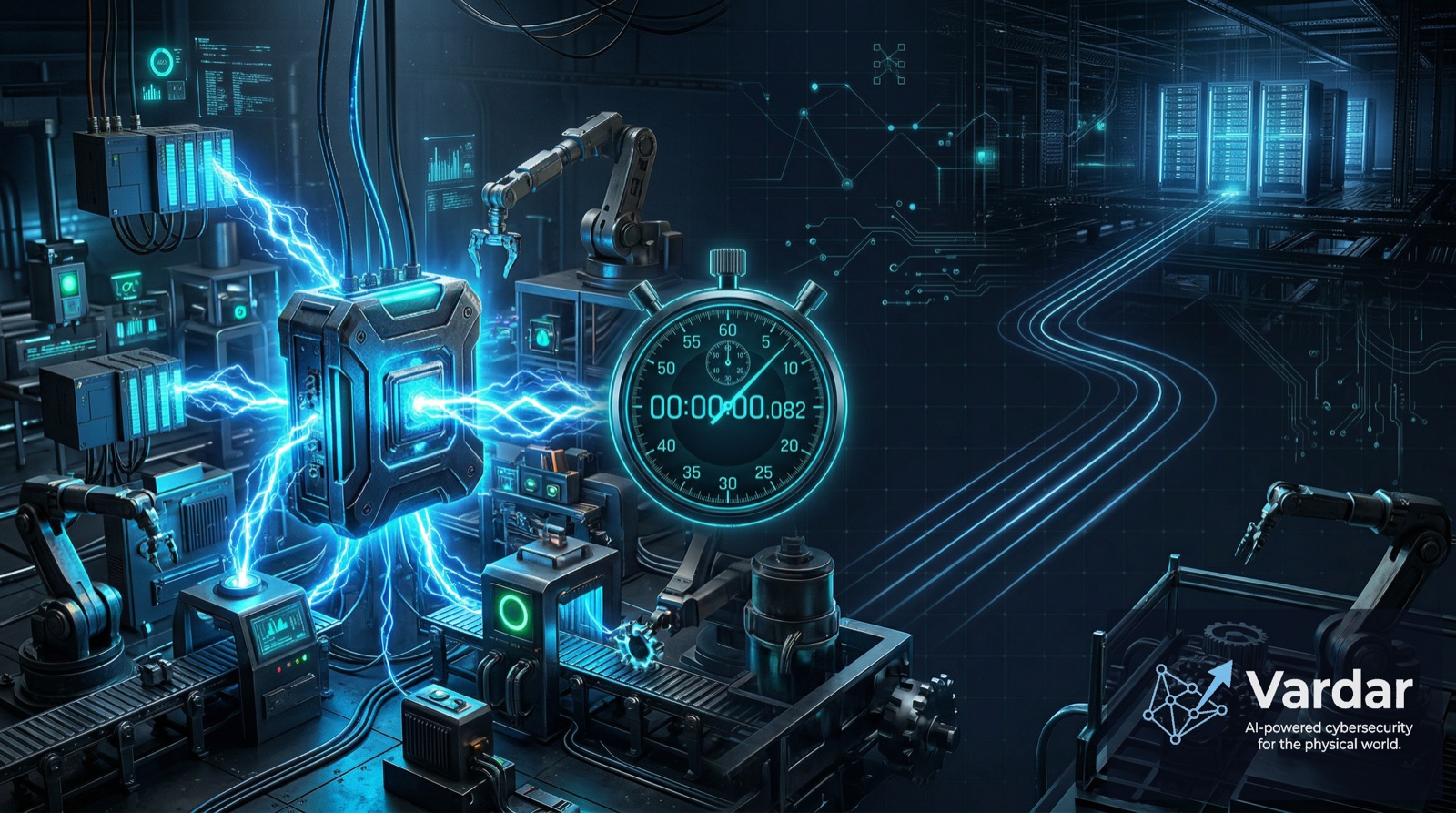
In OT environments, a detection delay of seconds can mean physical damage or safety incidents. Discover why edge AI is becoming the cornerstone of modern OT threat detection.

The EU's NIS2 Directive is redefining industrial cybersecurity. For IoT/OT organizations, 2026 is when compliance becomes real enforcement.

When an OT system goes down, the meter starts running at $125,000 per hour. But the invoice that follows is far larger than anyone expected.
Your network has more doors than you think — and most of them are wide open. Learn why IoT devices are the largest unprotected attack surface and how to close the gap.
A comprehensive guide to Operational Technology security — what it is, why it's different from IT security, and why every manufacturer needs it now.
Everything you need to know about NIS2 directive compliance for OT environments — key requirements, deadlines, and how to prepare your industrial network.
A deep dive into how machine learning models learn normal device behavior and detect threats that signature-based tools miss.