The Security Gap That Nobody Talks About
For the first time in history, cybersecurity ranks as the number one threat facing small and medium-sized businesses, overtaking long-standing economic concerns like inflation and recession according to VikingCloud's 2026 SMB Threat Landscape Report. Yet here is the paradox: 84% of SMBs self-manage their cybersecurity, and 28% report the person responsible lacks sufficient training.
The global SMB cybersecurity market is projected to reach approximately $25 billion by 2027, growing at 12-15% annually. But for small and mid-sized manufacturers, water treatment facilities, food processors, and logistics companies running OT environments, the security gap is even wider than these numbers suggest. Enterprise-grade OT security solutions were never designed for them. They require teams of specialists, months of deployment, and budgets that make CFOs flinch.
This is the accessibility crisis in OT security. And zero-touch deployment is how we solve it.
Why SMBs Are Uniquely Vulnerable
Small and medium industrial operations share a common profile: lean teams, tight budgets, and infrastructure that blends modern IT with legacy OT in ways that were never planned. The IT person — if there is one — wears multiple hats. The plant manager understands operations but not cybersecurity. And the equipment on the floor includes PLCs and controllers that were installed years before anyone worried about network security.
This creates a perfect storm of vulnerability:
No dedicated security staff. When 84% of SMBs self-manage cybersecurity, it means the person configuring the firewall is the same person troubleshooting the ERP system, ordering supplies, and resetting passwords. OT security expertise is a luxury these organizations cannot afford.
Legacy equipment with no upgrade path. Many SMBs run industrial equipment with 15-20 year lifespans. These devices cannot be updated, patched, or hardened. Compensating controls — network monitoring, segmentation, behavioral detection — are the only viable protection. But deploying those controls has traditionally required specialist skills.
Security tools designed for enterprises. Most OT security platforms assume the customer has a dedicated SOC, a team of analysts, and months for planning, deployment, and tuning. For an SMB with 50 employees and one IT generalist, this is an insurmountable barrier.
Growing regulatory pressure. NIS2's expanded scope pulls mid-sized manufacturers and service providers into mandatory cybersecurity obligations. The EU Cyber Resilience Act (CRA) adds requirements for connected products. Compliance is no longer optional, but the tools to achieve it remain out of reach for many smaller organizations.
SMBs face the same sophisticated threats as enterprises — the same ransomware crews, the same state-aligned actors pre-positioning in supply chains, the same hacktivists targeting exposed HMIs — but with a fraction of the resources to defend against them.
What Zero-Touch Deployment Actually Means
In the traditional OT security deployment model, a team of engineers spends weeks or months on-site: mapping the network, inventorying assets, configuring sensors, tuning detection rules, establishing baselines, and integrating with existing infrastructure. This model works for large enterprises with the budget and time to support it. For SMBs, it is a non-starter.
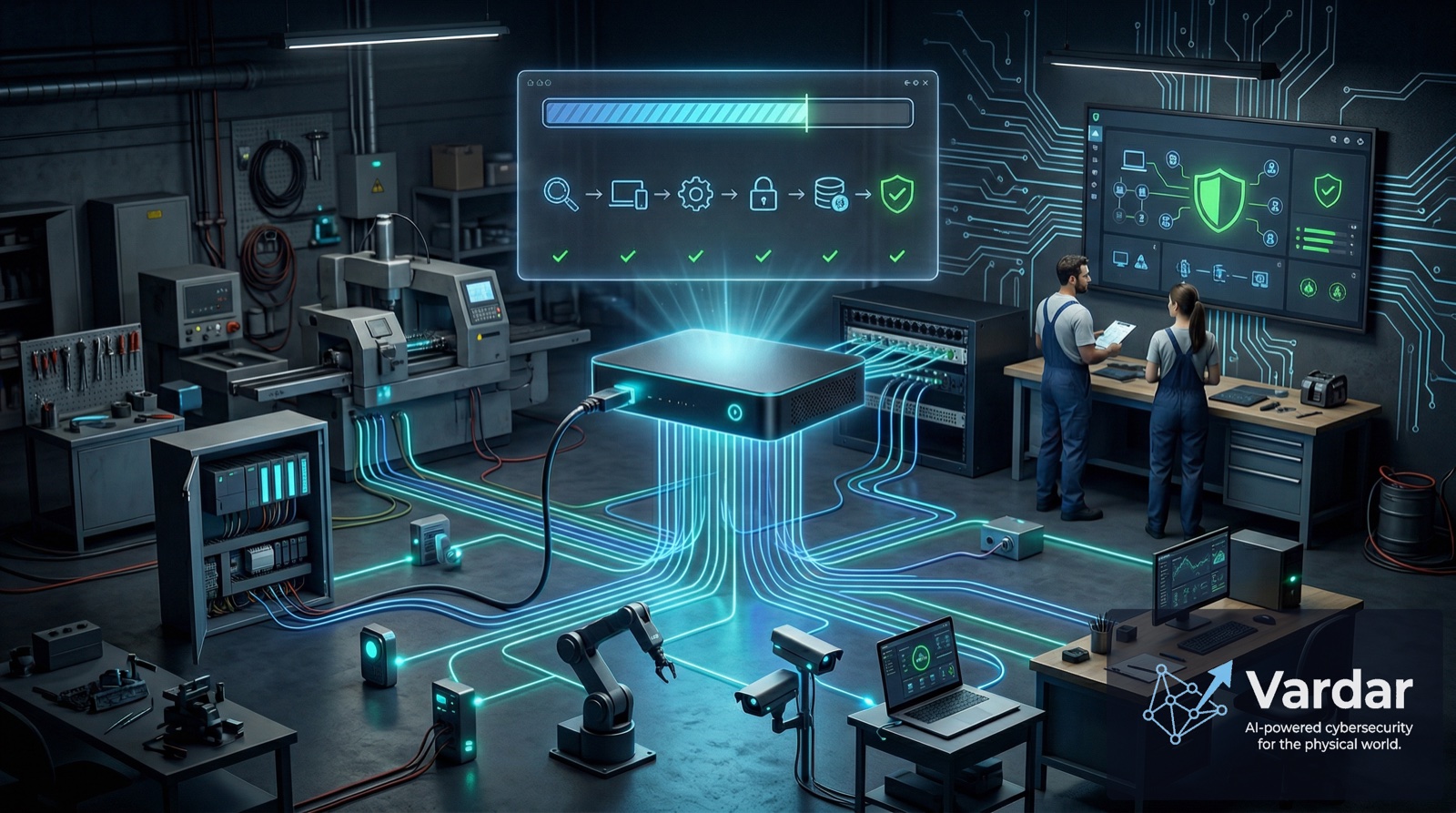
Zero-touch deployment inverts this model entirely. The concept is straightforward: a security solution that configures itself, learns the environment autonomously, and begins protecting from the moment it connects to the network — without requiring specialized expertise, extended professional services engagements, or complex configuration.
Here is what that looks like in practice:
Plug-and-protect deployment. The security appliance connects to the network and immediately begins passive discovery — identifying every device, mapping communication patterns, and building a complete asset inventory without any manual configuration.
Autonomous baseline learning. Using behavioral AI, the system establishes what "normal" looks like for each device, protocol, and communication pattern in the environment. This is not a static ruleset that a security engineer must define — it is a continuously evolving model that adapts to the specific operational reality of each facility.
Plain-language alerting. When the system detects an anomaly, it does not generate cryptic SIEM alerts that require a security analyst to interpret. It produces actionable, contextualized notifications that an OT engineer or plant manager can understand and act on immediately.
Automated compliance reporting. Instead of manually compiling evidence for NIS2 or CRA audits, the system continuously generates compliance documentation. One-click reports map the organization's security posture to regulatory requirements.
Zero-touch deployment compresses the OT security deployment timeline from months to minutes — eliminating the need for specialist teams and replacing complex configuration with autonomous learning.
The Democratization of OT Security
Zero-touch deployment is not just a convenience feature. It represents a fundamental shift in who can access effective OT security.
Consider the numbers: a traditional enterprise OT security deployment might cost hundreds of thousands of dollars in professional services alone, take 3-6 months, and require ongoing support from specialized staff. For an SMB with a total IT budget of perhaps $50,000-$100,000 per year, this model is impossible.
Zero-touch deployment compresses the timeline from months to minutes. It eliminates the need for specialized deployment teams. It replaces complex configuration with autonomous learning. And it translates security operations from expert-only activities into something a competent plant manager can handle.
Ready to Secure Your OT Network?
Get a free risk assessment of your industrial environment.
Request Free AssessmentAt Vardar, zero-touch deployment is a founding design principle, not a retrofit. Our Edge AI Sentinel connects to the network and begins protecting within minutes — discovering assets, learning behavioral baselines, and delivering actionable intelligence without any manual configuration. The dashboard speaks the language of operations, not cybersecurity. And our collective intelligence network means that even the smallest facility benefits from threat intelligence gathered across the entire Vardar ecosystem.
Because in 2026, the question is no longer whether SMBs need OT security. It is whether the security industry can deliver solutions that SMBs can actually use.