The Factory Floor Has Become a Battlefield
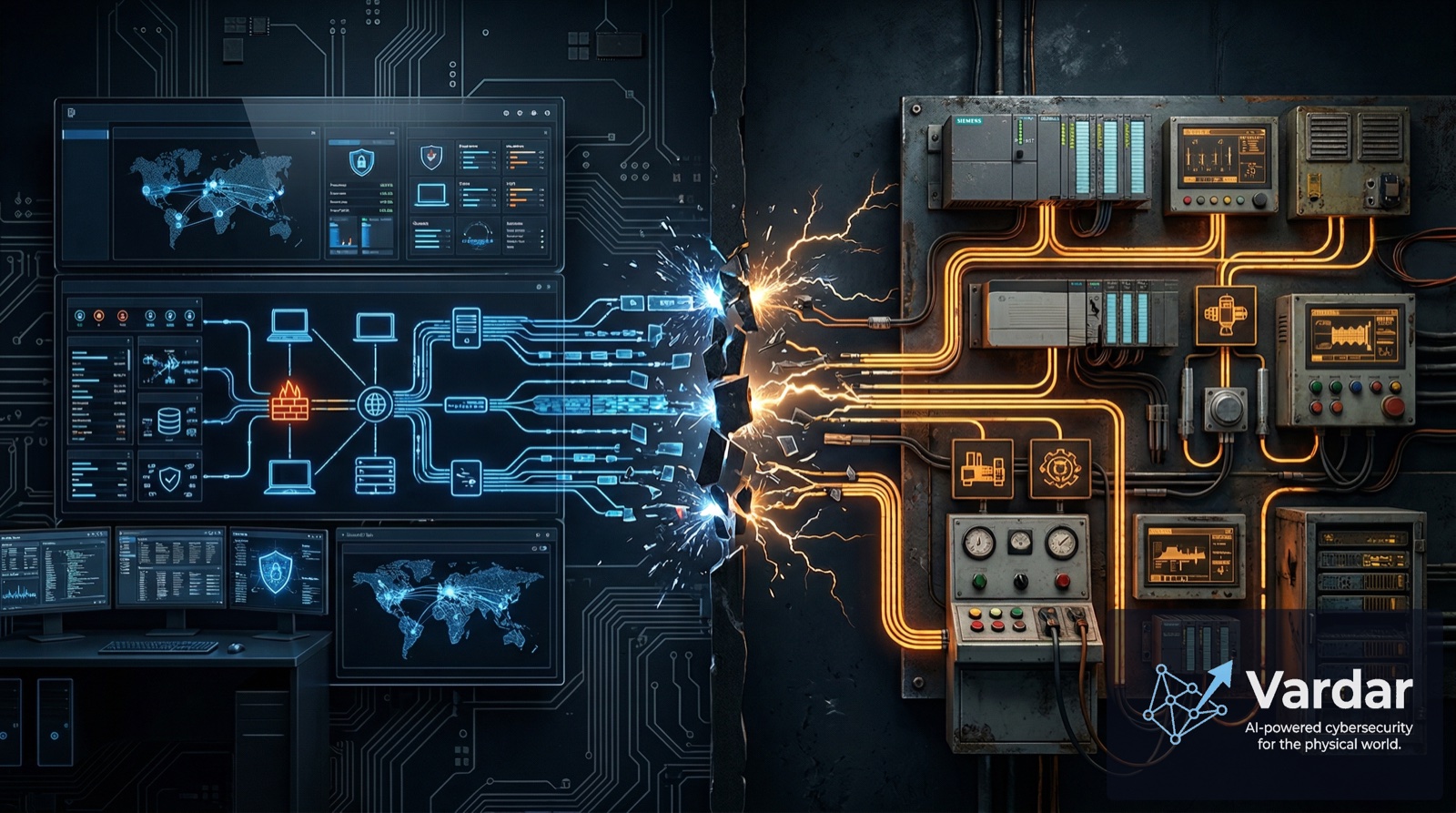
The smart factory revolution promised unprecedented efficiency: robotic assembly lines, real-time quality monitoring, predictive maintenance, and supply chains that practically run themselves. What nobody advertised was the cybersecurity bill that came with it.
For the fifth consecutive year, manufacturing was the most attacked industry globally, absorbing 27.7% of all cyberattacks according to IBM X-Force's 2025 report. ICS vulnerability disclosures nearly doubled from the previous year, hitting 2,451 across 152 vendors. And the median cost of a manufacturing ransomware incident now stands at $600,000 — not including the cascading supply chain damage that can multiply that figure many times over.
These are not abstract statistics. Behind every number is a factory floor that went dark, a production line that stopped, and engineers scrambling to understand what went wrong before it got worse.
Scenario 1: The Ransomware That Stopped the Line
The most common attack scenario in smart factories remains ransomware — and attackers have gotten surgical about it.
Modern ransomware crews no longer spray malware indiscriminately. They conduct weeks of reconnaissance, mapping the IT/OT boundary, identifying which systems control the most valuable production processes, and timing their strike for maximum impact. The entry point is typically mundane: a phishing email, a compromised VPN credential, or an exploited public-facing application (which accounted for 32% of manufacturing breaches last year).
Once inside the IT network, attackers move laterally until they reach the OT environment. In poorly segmented networks — still the norm in many manufacturing operations — this lateral movement encounters little resistance. The attackers then encrypt both IT systems (ERP, MES, supply chain management) and any Windows-based OT workstations, engineering stations, and historian servers they can reach.
The impact is immediate: production halts. Even if PLCs continue running their last programmed cycle, operators lose visibility and control. Without the MES to coordinate operations, without historians to track quality data, without engineering stations to modify programs — the factory is effectively blind.
This is precisely why ransomware gangs target manufacturing with such focus. Downtime is intolerable. Every hour of halted production costs tens of thousands to millions of dollars. The pressure to pay is immense.
Scenario 2: The Silent Process Manipulation
Far more dangerous than ransomware — though less visible — are attacks that manipulate industrial processes without triggering obvious alerts. Detecting them requires behavioral anomaly detection that understands what "normal" looks like at the protocol level — something traditional IT security tools cannot provide.
The Triton malware, which targeted safety instrumented systems, demonstrated this threat class years ago. But the approach has evolved. Today's sophisticated attackers use living-off-the-land techniques, valid credentials, and deep knowledge of industrial protocols to make subtle changes that look like normal operations.
Consider: an attacker who gains access to a PLC controlling a chemical mixing process could alter temperature setpoints by a few degrees, adjust flow rates by small percentages, or modify timing sequences just enough to produce out-of-spec product — all without tripping traditional alarm thresholds. The result might not be apparent for hours or days: degraded product quality, waste, customer complaints, or in the worst case, unsafe conditions that endanger workers.
This scenario is uniquely dangerous because it exploits the trust industrial operators place in their control systems. If the HMI shows normal values and no alarms are firing, operators assume the process is running correctly.
Scenario 3: Supply Chain Compromise at Scale
The third major threat scenario targets the smart factory's greatest strength — its interconnectedness — and turns it into a weapon.
Black Kite's 2025 Third-Party Breach Report revealed that third-party cyber incidents reached unprecedented scale: 136 major breaches affected 719 named companies and an estimated 26,000 additional downstream victims. The average number of downstream victims per breach reached 5.28 — the highest on record.
For smart factories, the supply chain attack surface is enormous. Every connected vendor system, every remote maintenance portal, every firmware update from an equipment supplier, and every cloud-based service represents a potential entry point. When attackers compromise a shared platform or high-dependency vendor, the impact cascades across every factory that relies on that service.
These attacks are particularly insidious because they abuse trust relationships. A firmware update from a trusted equipment vendor, a software patch from a SCADA supplier, or a routine data exchange with a logistics partner — all can serve as delivery mechanisms for malicious payloads. And with advanced persistent threats averaging 730 days before detection, the window for damage is staggering.
Scenario 4: Hacktivist Disruption of Exposed Systems
A rapidly growing threat that many manufacturers underestimate is hacktivism targeting industrial systems. Cyble's 2025 analysis documented a marked escalation, with groups like Z-Pentest, Dark Engine, and Sector 16 conducting repeated intrusions across a broad spectrum of industrial technologies.
These groups primarily target exposed HMIs and web-based SCADA interfaces — systems that should never be directly accessible from the internet but frequently are. Building management systems, IoT edge controllers, and VNC interfaces are also increasingly targeted.
Unlike state-sponsored actors who operate quietly, hacktivists often seek maximum visibility. They publish screenshots of compromised HMIs, claim responsibility on social media, and use disruption as a propaganda tool. While their technical sophistication varies, even basic access to an exposed HMI can cause real operational disruption — changing setpoints, disabling safety systems, or simply creating chaos that forces operators to shut down production as a precaution.
Ready to Secure Your OT Network?
Get a free risk assessment of your industrial environment.
Request Free AssessmentDefending the Smart Factory
Each of these scenarios shares common enablers: poor visibility, inadequate network segmentation, legacy systems that cannot be patched, and security tools that do not understand industrial environments.
Effective defense requires a purpose-built approach:
Continuous passive monitoring that understands industrial protocols at the application layer, detecting subtle anomalies in Modbus, EtherNet/IP, PROFINET, and other OT communications without risking operational disruption.
Behavioral baseline detection that learns what "normal" looks like for each device, process, and communication pattern — so that a two-degree temperature deviation or an unusual sequence of PLC commands triggers investigation before damage occurs.
Edge-processed intelligence that operates at millisecond speed, independent of cloud connectivity, ensuring detection and response continue even during network disruptions.
Collective threat intelligence shares anonymized attack patterns across deployments, so a novel technique detected at one factory immediately strengthens defenses everywhere else — the Waze model applied to OT security.
At Vardar, these capabilities are the foundation of our platform. Our Edge AI Sentinel monitors smart factory environments passively, detecting the full spectrum of threats — from ransomware lateral movement to subtle process manipulation to hacktivist intrusion — without agents, without cloud dependency, and without operational risk.