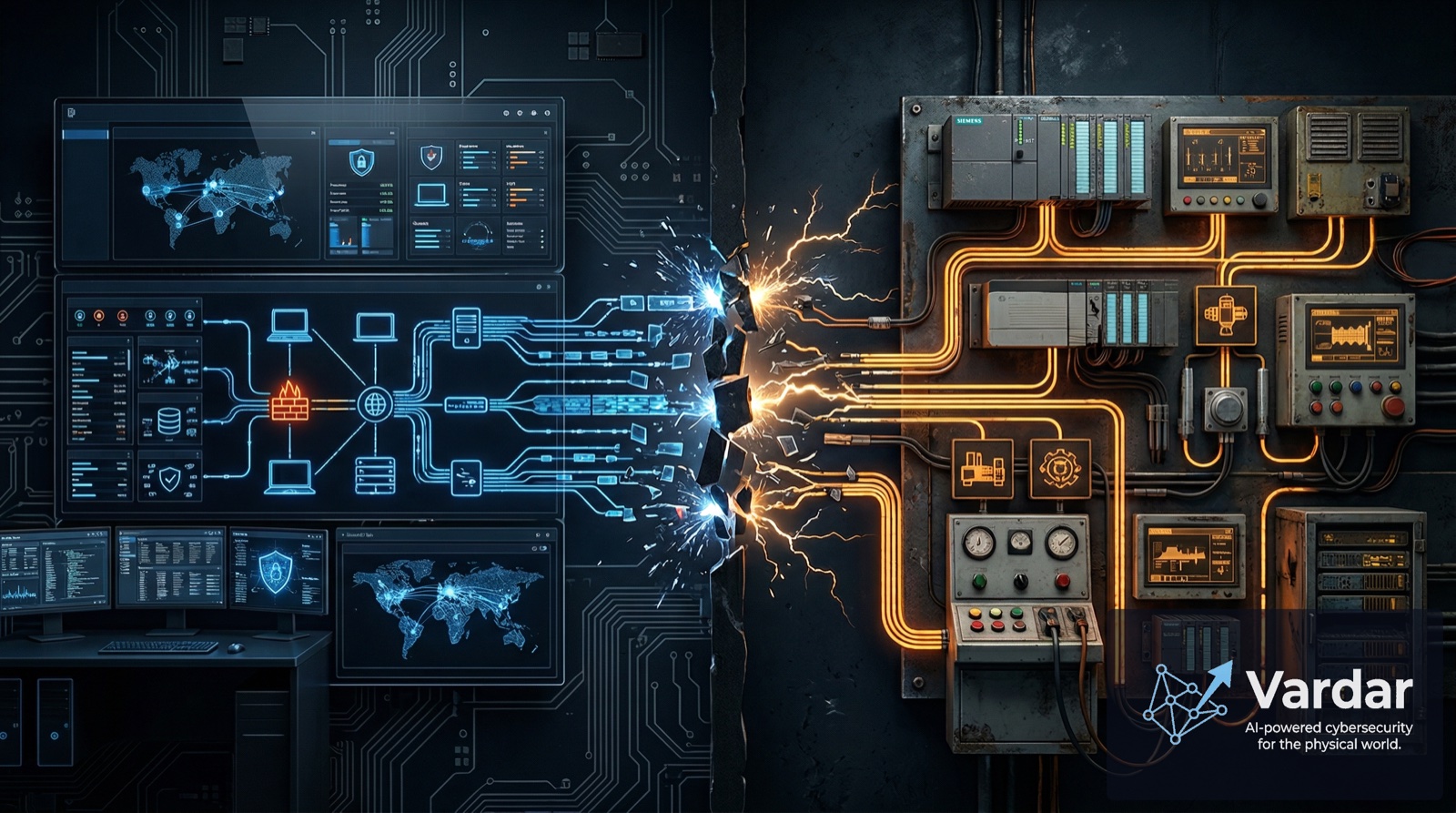
There is a persistent belief in many organizations that existing IT security tools — the firewalls, endpoint agents, vulnerability scanners, and SIEM platforms that protect corporate networks — can simply be extended to cover OT environments. It is a reasonable assumption on the surface. After all, networks are networks, right?
Wrong. And this assumption is getting organizations breached.
Trellix's latest Operational Technology Threat Report found that manufacturing accounts for 41.5% of detections and transportation and shipping 27.6%, with most attacks entering through IT infrastructure inside OT-focused organizations. The attackers are not using exotic exploits — they rely on PowerShell, Cobalt Strike, stolen credentials, and remote access tools to move laterally toward engineering assets. Once inside the right network segment, they shift to industrial protocols where traditional IT tools are blind.
In 2025, attacks exploiting OT protocols like Modbus jumped 84%, with Modbus alone seeing a 57% spike. These attacks succeed not because defenses are absent, but because the wrong defenses are in place.
The Fundamental Incompatibility
IT and OT environments operate under fundamentally different principles. IT prioritizes confidentiality, integrity, and availability — in that order. OT inverts the priority: availability and safety come first, with confidentiality often a distant concern. This difference permeates everything, from how devices communicate to how updates are applied.
Here is where traditional IT security tools break down in OT:
Endpoint agents cannot run on OT devices. Most PLCs, RTUs, HMIs, and industrial controllers lack the processing power, operating system support, or memory to host security agents. These devices run proprietary firmware and real-time operating systems designed for one purpose: controlling physical processes. Installing an agent risks destabilizing the device — and in OT, a crashed controller can halt a production line, shut down a power substation, or trigger a safety incident. As one OT security engineer put it, "What's routine for IT is sometimes dangerous or impossible in OT."
Active scanning disrupts operations. Vulnerability scanners that probe network devices work well in IT, where systems are designed to handle unexpected traffic. In OT, aggressive scanning has been documented causing PLCs to fault, HMIs to freeze, and communication stacks to crash. The Fortinet 2025 OT Security Report revealed that 50% of OT organizations experienced breaches last year despite actively advancing their security programs — partly because the tools they deployed were designed for a different environment.
IT threat intelligence misses OT-specific threats. Standard threat feeds focused on malware signatures, phishing domains, and botnet infrastructure do not account for the industrial protocols and decades-old communication standards that dominate OT. Tools like Triton, Industroyer, and FrostyGoop — malware purpose-built to manipulate physical processes — use techniques that look like normal OT traffic to IT-centric security platforms. They manipulate Modbus registers, send forged DNP3 commands, or abuse IEC 61850 communications in ways that only protocol-aware inspection can detect.
Alert volumes overwhelm OT teams. IT security tools generate massive volumes of alerts calibrated for environments with dedicated SOC teams. OT environments typically have lean security staff — sometimes just one engineer covering an entire plant. When an IT SIEM floods these teams with thousands of alerts, most of which are false positives irrelevant to industrial operations, alert fatigue sets in quickly. Critical signals get lost in the noise.
The Visibility Catastrophe
Perhaps the most damaging failure is in visibility. Traditional IT tools cannot properly discover and inventory OT assets because they do not understand industrial protocols. A corporate network scanner might see an IP address and a MAC address, but it cannot tell you the specific PLC model, firmware version, configuration state, or whether it is running an authorized program.
This matters enormously. An analysis of nearly one million OT devices found that 40% of organizations had devices with known, actively exploited vulnerabilities that were insecurely connected to the Internet. Seven percent of devices harbored vulnerabilities linked to active ransomware campaigns. Without granular, protocol-aware asset visibility, organizations cannot even begin to assess their true risk.
Industry researchers estimate that less than 5% of global OT networks have comprehensive security monitoring. In enterprise IT, that statistic would be unimaginable. In OT, it is the current reality — and traditional IT tools, no matter how sophisticated, cannot close that gap because they were never designed to speak the language of industrial systems.
What OT Networks Actually Need
Effective OT security requires a fundamentally different approach — one designed from the ground up for industrial environments:
Agentless, network-based detection. Instead of installing software on fragile OT devices, monitoring must happen passively at the network layer. By inspecting traffic without modifying or querying devices, security tools can maintain real-time awareness without risking operational disruption. This is not a compromise — it is the only safe approach for most OT environments.
Deep protocol awareness. Security platforms must understand Modbus, DNP3, EtherNet/IP, PROFINET, BACnet, and dozens of other industrial protocols at the application layer. Only with this depth can a security tool distinguish between a legitimate operator command and a malicious injection — a distinction invisible to generic packet inspection.
OT-contextualized alerting. What is anomalous in IT may be perfectly normal in OT, and vice versa. Effective monitoring must establish behavioral baselines specific to each industrial process, device role, and communication pattern. Alerts must be tuned for OT reality: fewer, higher-confidence, and immediately actionable by engineers who may not have deep cybersecurity expertise.
Operational continuity as a design principle. Every aspect of the security solution — from deployment to monitoring to response — must respect OT's non-negotiable requirement for uptime. Zero-touch deployment, passive monitoring, and automated containment that does not disrupt processes are not nice-to-haves. They are prerequisites.
At Vardar, we built our platform specifically because we understood this gap. Our Edge AI Sentinel operates passively at the network layer, understanding industrial protocols natively and establishing behavioral baselines unique to each environment. It deploys without touching a single OT device, generates contextualized alerts designed for lean OT teams, and processes everything at the edge — no dependency on cloud connectivity, no latency, no data leaving the facility.
Ready to Secure Your OT Network?
Get a free risk assessment of your industrial environment.
Request Free AssessmentStop Trying to Make IT Tools Work in OT
The organizations achieving the best security outcomes in 2026 are not the ones spending more on traditional IT security. They are the ones deploying purpose-built OT solutions alongside their IT stack, creating unified visibility without forcing incompatible tools into environments where they create more risk than they mitigate.
The IT/OT convergence is real and accelerating. The security approach must converge too — but that means building bridges between purpose-built tools, not hammering IT solutions into OT-shaped problems.